The Shift That’s Coming
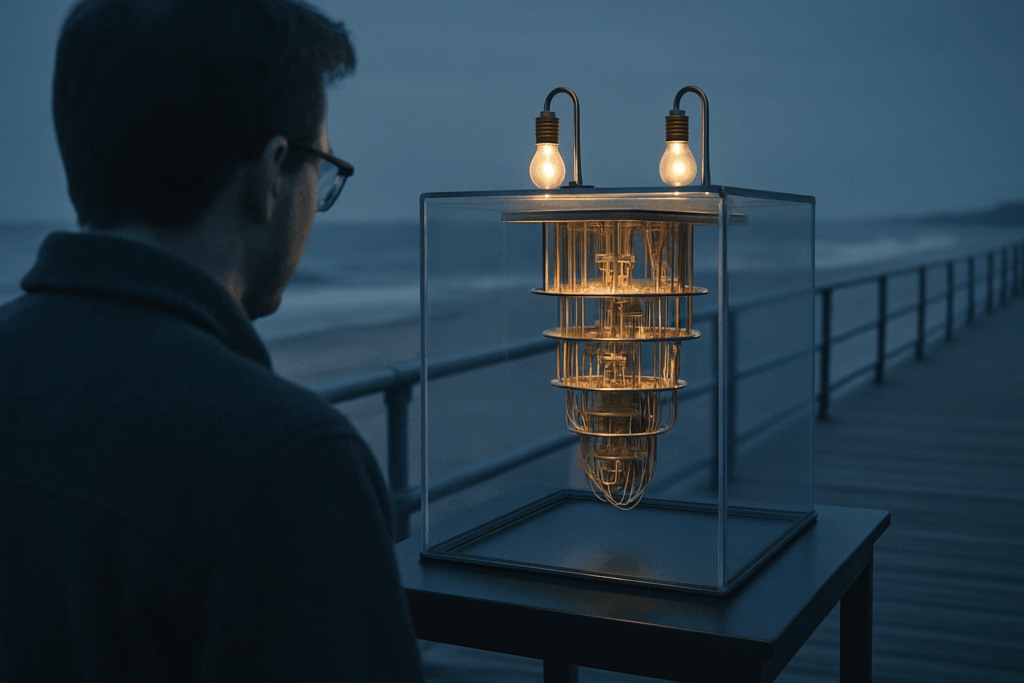
Quantum computing isn’t just a faster version of traditional machines it’s a full rewrite of how information can be processed. Instead of bits (0s and 1s), quantum computers use qubits. Qubits can exist in a blend of states, thanks to quantum properties like superposition and entanglement. In theory, this lets them tackle certain problems that would take classical computers years if not centuries to solve.
But let’s be clear: quantum computing isn’t magic. It won’t replace your phone or solve all of our energy problems overnight. It’s not great for everything just exceptionally good for a specific class of problems, including cracking encryption, simulating molecular interactions, and optimizing complex systems.
So where are we in 2026? We’re past the hype of “quantum supremacy” headlines and entering the grind phase. Big players like IBM, Google, and several governments now have prototype quantum systems with 100+ qubits, and error correction is inching forward. Still, we’re far from scalable, fault tolerant quantum computers powerful enough to upend security or industry at large. Experts say we have a decade maybe less before quantum gets practical. Translation: the clock is ticking.
Breaking the Locks: Classical Encryption Under Threat
RSA and ECC two of the pillars of modern cryptography are built on the idea that certain math problems are just too hard to solve with current technology. RSA, for example, relies on the difficulty of factoring large numbers, while ECC (Elliptic Curve Cryptography) counts on the complexity of solving discrete logarithms. These problems stump the best classical algorithms, even with supercomputers. But quantum computing changes that.
Enter Shor’s Algorithm. It’s not science fiction it’s a quantum algorithm discovered in the 1990s that, once run on a sufficiently powerful quantum machine, can factor large numbers exponentially faster than classical methods. In simple terms: what would take thousands of years on today’s hardware might be cracked in hours or minutes on a quantum machine. Same goes for ECC. This puts a giant clock over every encrypted email, transaction, or private message protected by those systems.
The real danger? Harvest now, decrypt later attacks. Adversaries don’t need to break encryption today. They just need to collect sensitive data and wait. Once quantum machines are mature which could happen as early as the 2030s everything stored using RSA or ECC could become readable.
This isn’t a drill. Governments, financial institutions, and health organizations are already preparing. The timeline is tight, because the data at risk isn’t just in the future it’s everything that’s already been captured.
Quantum Resistant Encryption
Post quantum cryptography (PQC) isn’t magic it’s math. As quantum computers creep toward real world capability, PQC is the practical counterpunch: encryption algorithms built to resist quantum attacks. In plain terms, these algorithms are designed so even a powerful quantum machine as imagined by current physics can’t solve them in any reasonable amount of time.
The U.S. National Institute of Standards and Technology (NIST) has been leading the charge, and in 2026 it finalized its first round of approved post quantum algorithms. Among them: CRYSTALS Kyber (for key encapsulation) and CRYSTALS Dilithium (for digital signatures). These aren’t just lab tested they’re vetted, peer reviewed, and ready to be implemented at scale. NIST also continues to update guidance as more testing sheds light on edge cases and performance quirks.
Governments and financial institutions aren’t waiting around. In the U.S., federal agencies began quantum safe pilots as early as 2023. Today, trial deployments include encrypted communications between departments, quantum safe VPNs, and secure financial messaging standards. Banks and major cloud providers are integrating PQC into their infrastructure not across the board yet, but enough to say it’s moved from theoretical to operational.
Quantum resistant encryption isn’t hype. It’s happening, and smart players are already building with it.
It’s Not All Doom

Quantum computing is often painted as a looming threat to cybersecurity, but the full picture is more nuanced. Yes, it disrupts current cryptographic systems but it also introduces opportunities to make data protection more robust.
Security Through Physics: What is Quantum Key Distribution (QKD)?
Unlike traditional encryption methods that rely on complex algorithms, QKD leverages fundamental principles of quantum mechanics to establish secure communication channels. At its core, QKD allows two parties to generate a shared, secret cryptographic key one that cannot be intercepted without detection.
Key aspects of QKD:
Measurement disturbs the system: Any attempt to eavesdrop on a quantum key alters its state, alerting users to a breach.
True randomness: Quantum systems generate keys that are impossible to predict using classical methods.
Use of quantum entanglement: Certain protocols use entangled particles to verify communication security.
While still in early stages of deployment, QKD has already seen real world applications in sectors highly sensitive to data breaches.
When Quantum Security Becomes a Strength
Though the conversation often focuses on what quantum computing breaks, it also opens doors to making cybersecurity systems smarter, faster, and more forward compatible.
Scenarios where quantum enhanced security benefits systems include:
Securing high value data in transit, especially for government and military operations
Improving authentication protocols by blending classical and quantum derived keys
Building trust in zero trust environments using quantum generated credentials
These approaches don’t just defend against future threats they raise the bar for what’s considered secure communication today.
Real World Applications Already Taking Shape
Quantum security is not just theoretical. It’s already being piloted and selectively implemented in industries where stakes are high and long term data confidentiality is non negotiable.
Sectors actively exploring or integrating quantum security include:
Defense: Governments are testing QKD for secure command and communications systems between critical assets
Biotech and Pharma: Protecting intellectual property and clinical trial data using quantum safe encryption
Financial Services: Early trials of cryptographic infrastructure designed to withstand post quantum threats
These real world use cases signal that quantum safe methods are not only possible they’re becoming necessary.
What Businesses Should Do Now
There’s no countdown clock for quantum decryption, but that doesn’t mean you can wait. Data being collected today especially long life, high value assets is already at risk. Think medical records, intellectual property, government communications, banking credentials. If it’s sensitive, assume someone’s storing it to crack later when quantum hits maturity. That’s why security pros call it a harvest now, decrypt later problem.
Start by creating a data classification map. Identify what’s mission critical and long lived. If it needs to stay private for 10+ years, it’s a candidate for quantum resilient protection.
Next: hybrid encryption. This is your bridge. You don’t need to rip out classical cryptography overnight. Instead, layer in quantum safe algorithms alongside existing ones. Organizations like NIST have already recommended vetted methods, and leading vendors are supporting these dual systems in select offerings.
As the tech evolves, so will the market noise. Watch for snake oil. Be wary of vendors yelling “quantum proof” without showing test data, NIST alignment, or peer reviewed results. Ask them directly: What quantum safe algorithms are you using? Can you support hybrid implementation? How do you plan to handle updates as standards evolve?
Security teams don’t need to have all the answers today but they do need to be asking the right questions. Quantum isn’t a surprise anymore. It’s a deadline.
How It Ties Into Emerging Infrastructure
Quantum security isn’t just a cloud problem. The rise of edge computing a system where devices process data locally instead of sending everything back to centralized servers makes the stakes even higher. From smart thermostats to connected vehicles, edge devices are everywhere and often operate with minimal oversight. If they’re not secured against quantum threats, they become the back door every attacker dreams of.
The issue? Most IoT and edge devices still rely on outdated encryption. Once quantum computers become capable of breaking RSA or ECC, any captured data even from today could be cracked. And edge nodes, by design, can’t afford the same high latency defense systems available to backend data centers. The solution is quantum safe local processing: lightweight, resilient cryptographic protocols that can run on small chips while resisting next gen threats.
Networks need hardening now. Most IoT devices installed today will still be functional when quantum threats go live. That means prepping today’s firmware, update channels, and network architecture to scale toward quantum resistance. Skipping that prep invites disaster.
For context on the direction the edge ecosystem is headed, check out The Rise of Edge Computing and its Role in IoT Expansion.
Watch This Space
Quantum computing is moving out of theory and into application and a range of global players are accelerating the pace. From corporate labs to government funded initiatives, the next wave of breakthroughs could redefine how the world handles secure data.
Leaders in the Quantum Race
Several organizations are shaping the quantum landscape, each bringing unique capabilities:
IBM Invested heavily in superconducting qubits and quantum as a service platforms; already working with multiple Fortune 500 firms.
China A growing powerhouse in quantum research, particularly in satellite based quantum communication and breakthroughs in QKD (Quantum Key Distribution).
Startups Companies like Rigetti, IonQ, and PsiQuantum are driving innovation with niche hardware approaches and cloud based access models.
Academic Research Universities globally, like MIT, TU Delft, and the University of Science and Technology of China, continue to push theoretical and applied research forward.
What to Watch in the Next 18 24 Months
The pace of quantum development can be unpredictable, but a few key milestones are worth keeping an eye on:
NIST Final Standards Official approval and rollout of post quantum cryptographic (PQC) standards.
Quantum Hardware Scaling Progress toward fault tolerant, error corrected quantum systems.
Private Sector Deployment Use cases in banking, logistics, and healthcare showing real world quantum advantage.
International Policy Emerging legal frameworks around quantum export controls and cybersecurity obligations.
Why It Matters by 2030
Quantum readiness isn’t just about responding to threats it’s about gaining strategic advantage. By proactively engaging in quantum safe practices now, organizations can:
Protect sensitive data with long term value (e.g., health records, proprietary research).
Reduce future compliance costs by aligning early with global PQC standards.
Lead in trust building, offering clients and users forward proofed security.
By 2030, the businesses best prepared for the quantum shift won’t be those that reacted last minute, but those that built adaptability and awareness into their security culture today.